Private Browsing
Sometimes we may have to use the Internet on a computer or a telephone device other than ours for an emergency or urgent matter, or because our device is not available or for any other reason.
However, when we browse the Internet on any device, the device retains the names and addresses of the sites we visited, as well as the data we have entered, such as the personal data that we enter on a form, electronic request or the e-mail addresses we used.
In order to get rid of this data, we must delete the websites history and data stored on the browser, this may be unavailable for several reasons, the most important ones is that we will delete the websites addresses and data of the owner of the device, on the other hand not knowing how to delete this data and information.
Instead, the companies producing the most popular Internet browsers, “Firefox” and “Chrome” put a feature inside the browser, which automatically deletes the history and data of all sites we visited.
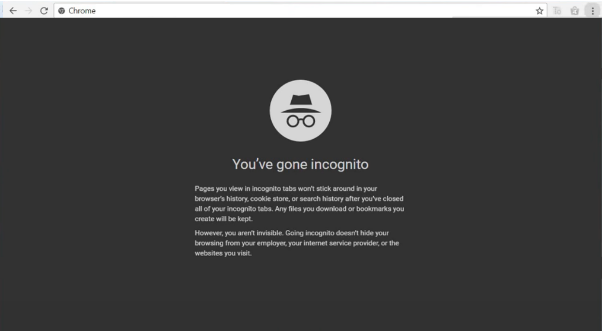
By creating something called “private browsing or incognito”
What is private browsing or incognito?
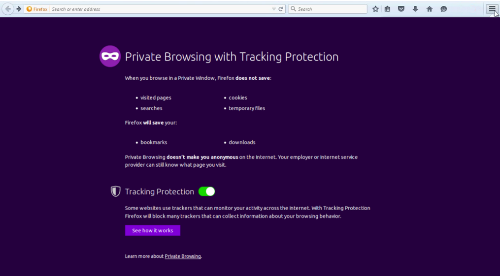
It is a “window” of the browser, which works exactly as the browser does with all its features, but it is distinct from it, that when you close the browser it deletes the history of the visited sites and the data entered by it.
* Private or incognito browsing deletes only the history of sites visited from private or incognito browsing and does not delete the history of visited sites from your regular browser.
How do I access Incognito?
Firefox
From within your browser
- Click on the icon at the top
 of your browser
of your browser - Click on “New Private Window”
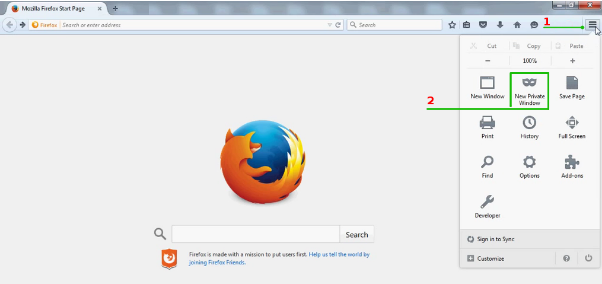
A new window opens
On Chrome
From within your browser
- Click on the icon
 at the top of your browser
at the top of your browser - Click on the “New incognito window” option.
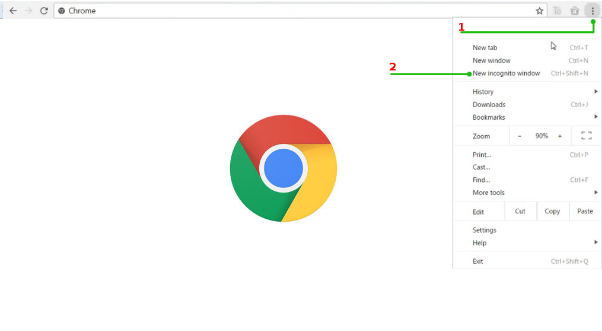
A new window opens
*important note
To the extent possible, avoid the use of other people’s computers or telephone devices, especially those which belongs to public places (Internet cafes, hotels, libraries…) for fear that these devices will be equipped with monitoring and recording programs for activities that take place on the device, including recording accounts data (Username and password).
End